This is an old revision of the document!
Table of Contents
Capturing DUML
Capturing DUML packets can be tricky if you are new to the scene. This page is designed to list some of the easy ways to capture DUML. It will grow over time as other people document other methods.
A. Mac Capture with WireShark
1. Disable SIP
- Restart your Mac
- Hold down Command-R to reboot into Recovery Mode
- Click Utility » Terminal, type “csrutil disable”, click Enter.
- Restart your Mac
2. Bring up the USB interface for DUML traffic
sudo ifconfig XHC20 up
NOTE: When not required for capturing, you should disable this interface using the following command.
sudo ifconfig XHC20 down
3. Capture
Capture from the XHC20 interface using Wireshark. USB capture filters are unsupported, so you will get lots of garbage mixed in with the DUML.
4. Filter
To view only the interesting traffic, the following filter is what worked for me.
frame.protocols == "usb" && usb.darwin.request_type == 1 && usb.bInterfaceClass == 0x0a && frame.len > 32
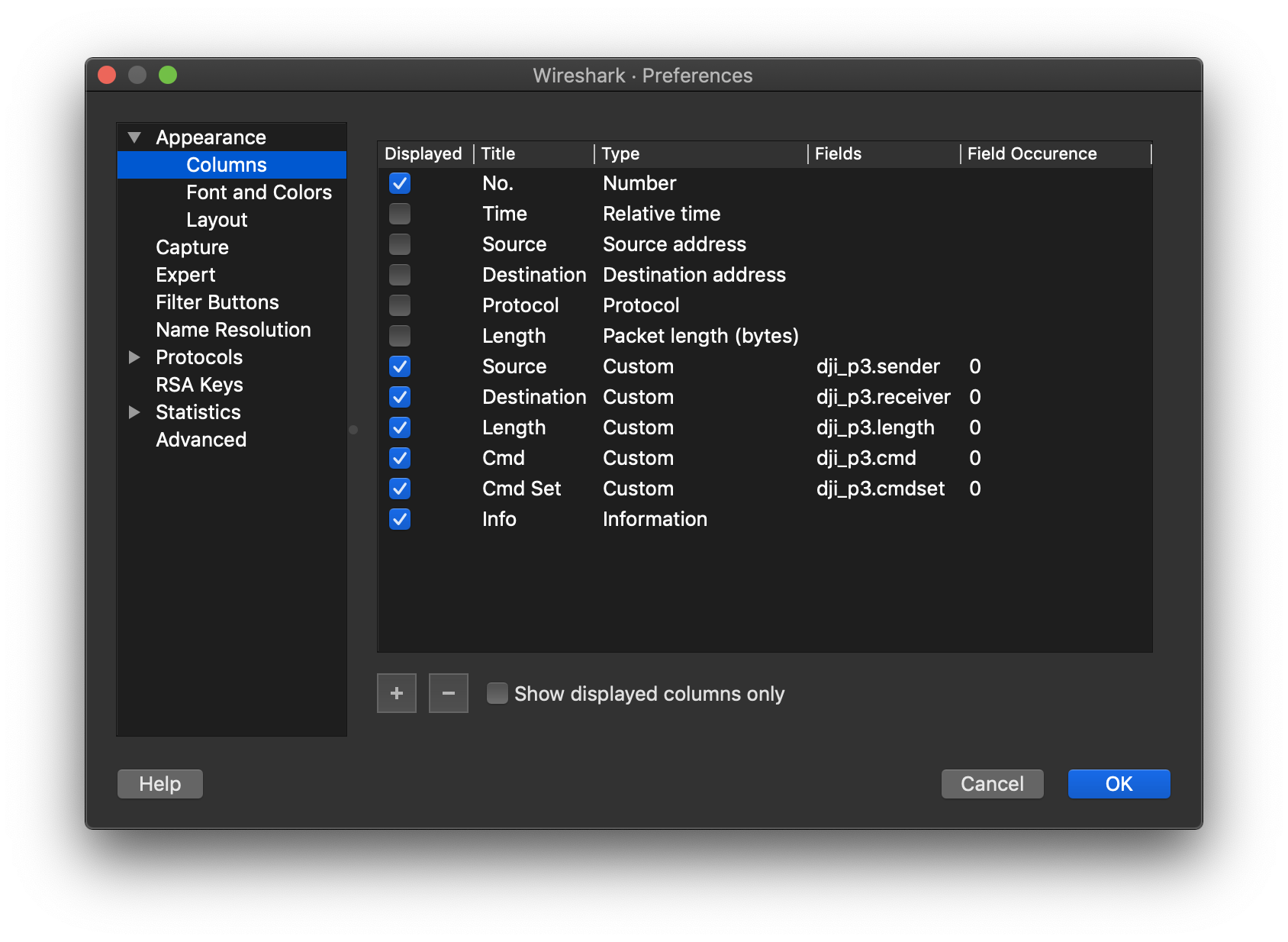
B. Wireshark Dissectors - MacOS
Now that we have some data, we need to understand what it is saying. Thankfully, @mefisto has created Wireshark DUML packet dissectors which make it easy to interpret DUML packets. To read his full detailed instructions, go to his GITHUB page.
I am providing additional data here to help provide clarity if you have tried and been unsuccessful in using the dissectors. But before I start, let me tell my story.
In my case, I installed all of the LUA files, restarted Wireshark. But nothing changed. I assumed there were other tasks to do in order to get it to work - perhaps to strip off the USB layer. I came back to the task the next day, and without making any further changes - things just started working. (Mostly). The dissectors were displaying the breakdown of all of the sub-fields. There is a small percentage of packets that were and are still causing errors. This issue is still outstanding. So I will come back to this topic later.
But how did it start mostly working overnight? It turned out that the dissectors are heuristic dissectors. I thought I was going to have to manually strip the USB header, but they worked out the DUML embedded inside the USB packets. What changed? I have no idea. Anyway, onto what I did for the setup.
1. Install Wireshark
I am using version 3.4.9. Just install from the appropriate package for your computer.
2. Install the dissectors
If the only thing you need is the dissectors, you could follow the guide below. Make your own arrangements to pull down from Github if you want to use other components. NOTE: The commands below will append the new details into any existing init.lua file. A backup is created in case of any issues.
mkdir /tmp/mefisto cd /tmp/mefisto git clone https://github.com/o-gs/dji-firmware-tools.git cp ~/.config/wireshark/init.lua ~/.config/wireshark/init.lua.bak cp dji-firmware-tools/comm_dissector/wireshark/dji*lua ~/.config/wireshark/ cat dji-firmware-tools/comm_dissector/wireshark/init.lua >> ~/.config/wireshark/init.lua cd /tmp rm -rf mefisto
3. Restart Wireshark and capture
Start a packet capture in Wireshark, from the XHC20 interface.
4. Set a display filter
(frame.protocols == "usb" && usb.darwin.request_type == 1 && usb.bInterfaceClass == 0x0a && frame.len > 32) or dji_dumlv1
This filter is designed to capture all valid dji_dumlv1 packets, but also to capture any poorly decoded packets to allow you to look at the cause of any problems with the dissectors.